Hackers built a seemingly benign bridgehead app, which establishes connection to the victim's device. It had managed to bypass Google protection, and some apps have been sitting in the Play Store for months. Once the ad gets a click, the malware author receives payment from the website developer.
Check Point, in a blogpost, describes it as an auto-clicking adware that has been found on 41 apps developed by a Korean company Kiniwini. There are a handful of apps from other developers too. It uses infected devices to generate false clicks on advertisements, further generating revenues for the perpetrators behind it.

It had managed to bypass Google protection. Hackers built a seemingly benign bridgehead app, which establishes connection to the victim's device and further inserts it into the app store.
As an Android user, you have to start taking security seriously. To know if your device is infected, check the list below to find out if you have downloaded one of these apps. Also, steer clear from downloading these apps.
Here's the complete list of infected apps:
Apps by Kiniwini
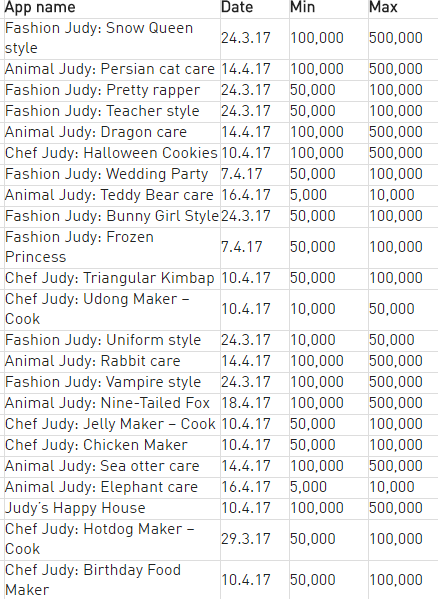
More apps by Kiniwini

Infected apps from other developers

Google Play Store has numerous apps listed and most are free to use. However, one has to be sure that the app is from a reliable developer or known company before downloading it. Take a closer look at app permissions, and ensure you are not giving away too much of private information. If there is an update on your device from Google, ensure that you install it.
Most of us look up for free Wi-Fi when travelling, but one must ensure not to share any private information. It is important to install a reliable anti-virus on your device that will alert about malware, malicious links and so on. You can take a look at 5 best free anti-virus solutions for your Android device here.
