Hackers built a seemingly benign bridgehead app, which establishes connection to the victim's device and further inserts it into the app store. It had managed to bypass Google protection, and some apps have been sitting in the Play Store for months. Once the ad gets a click, the malware author receives payment from the website developer.
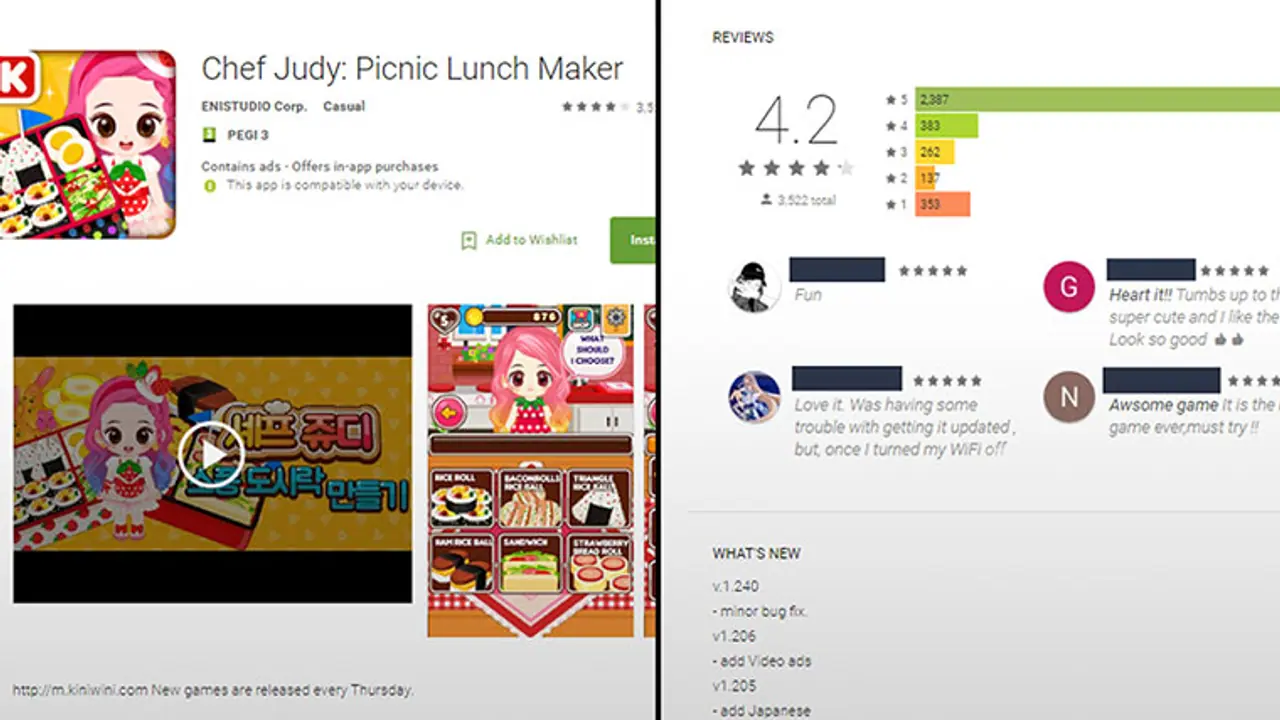
Check Point, in a blogpost, describes it as an auto-clicking adware that has been found on 41 apps developed by a Korean company. It uses infected devices to generate false clicks on advertisements, further generating revenues for the perpetrators behind it.

It had managed to bypass Google protection. Hackers built a seemingly benign bridgehead app, which establishes connection to the victim's device and further inserts it into the app store.
"Once a user downloads a malicious app, it silently registers receivers which establish a connection with the C&C server. The server replies with the actual malicious payload, which includes JavaScript code, a user-agent string and URLs controlled by the malware author. The malware opens the URLs using the user agent that imitates a PC browser in a hidden webpage and receives a redirection to another website. Once the targeted website is launched, the malware uses the JavaScript code to locate and click on banners from the Google ads infrastructure," Check Point explains.
Once the ad gets a click, the malware author receives payment from the website developer. The malicious apps have been developed by a Korean company named Kiniwini, which is registered on Google Play as ENISTUDIO corp. It builds apps for both Android and iOS. Judy displays too many ads, which sometimes leaves users with no option but clicking on the ad itself. According to online reports, Google has begun pulling out infected apps.
Earlier this month, Check Point had revealed how hackers can use malicious subtitles to gain access of your PC. The list of effected media players includes VLC, Popcorn Time, Kodi and Stremio.